Signing commits with GPG
- Introduced in GitLab 9.5.
- Subkeys support was added in GitLab 10.1.
You can use a GPG key to sign Git commits made in a GitLab repository. Signed commits are labeled Verified if the identity of the committer can be verified. To verify the identity of a committer, GitLab requires their public GPG key.
NOTE: Note: The term GPG is used for all OpenPGP/PGP/GPG related material and implementations.
GPG verified tags are not supported yet.
See the further reading section for more details on GPG.
How GitLab handles GPG
GitLab uses its own keyring to verify the GPG signature. It does not access any public key server.
For a commit to be verified by GitLab:
- The committer must have a GPG public/private key pair.
- The committer's public key must have been uploaded to their GitLab account.
- One of the emails in the GPG key must match a verified email address used by the committer in GitLab.
- The committer's email address must match the verified email address from the GPG key.
Generating a GPG key
If you don't already have a GPG key, the following steps will help you get started:
-
Install GPG for your operating system. If your Operating System has
gpg2installed, replacegpgwithgpg2in the following commands. -
Generate the private/public key pair with the following command, which will spawn a series of questions:
gpg --full-gen-keyNOTE: Note: In some cases like Gpg4win on Windows and other macOS versions, the command here may be
gpg --gen-key. -
The first question is which algorithm can be used. Select the kind you want or press Enter to choose the default (RSA and RSA):
Please select what kind of key you want: (1) RSA and RSA (default) (2) DSA and Elgamal (3) DSA (sign only) (4) RSA (sign only) Your selection? 1 -
The next question is key length. We recommend you choose
4096:RSA keys may be between 1024 and 4096 bits long. What keysize do you want? (2048) 4096 Requested keysize is 4096 bits -
Specify the validity period of your key. This is something subjective, and you can use the default value, which is to never expire:
Please specify how long the key should be valid. 0 = key does not expire <n> = key expires in n days <n>w = key expires in n weeks <n>m = key expires in n months <n>y = key expires in n years Key is valid for? (0) 0 Key does not expire at all -
Confirm that the answers you gave were correct by typing
y:Is this correct? (y/N) y -
Enter your real name, the email address to be associated with this key (should match a verified email address you use in GitLab) and an optional comment (press Enter to skip):
GnuPG needs to construct a user ID to identify your key. Real name: Mr. Robot Email address: <your_email> Comment: You selected this USER-ID: "Mr. Robot <your_email>" Change (N)ame, (C)omment, (E)mail or (O)kay/(Q)uit? O -
Pick a strong password when asked and type it twice to confirm.
-
Use the following command to list the private GPG key you just created:
gpg --list-secret-keys --keyid-format LONG <your_email>Replace
<your_email>with the email address you entered above. -
Copy the GPG key ID that starts with
sec. In the following example, that's30F2B65B9246B6CA:sec rsa4096/30F2B65B9246B6CA 2017-08-18 [SC] D5E4F29F3275DC0CDA8FFC8730F2B65B9246B6CA uid [ultimate] Mr. Robot <your_email> ssb rsa4096/B7ABC0813E4028C0 2017-08-18 [E] -
Export the public key of that ID (replace your key ID from the previous step):
gpg --armor --export 30F2B65B9246B6CA -
Finally, copy the public key and add it in your profile settings
Adding a GPG key to your account
NOTE: Note: Once you add a key, you cannot edit it, only remove it. In case the paste didn't work, you'll have to remove the offending key and re-add it.
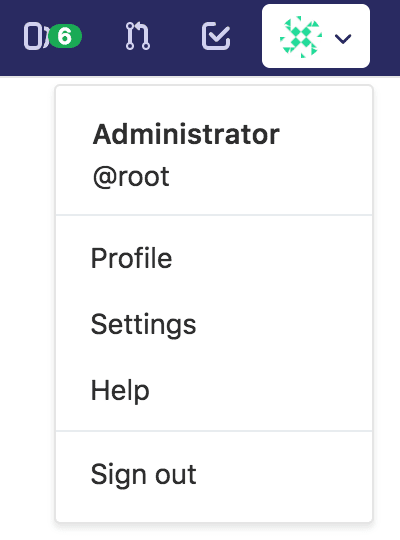
You can add a GPG key in your profile's settings:
-
On the upper right corner, click on your avatar and go to your Settings.
-
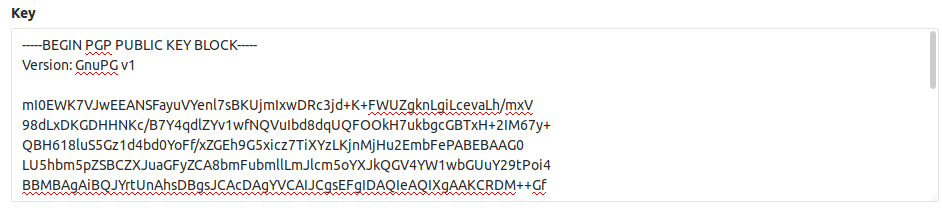
Navigate to the GPG keys tab and paste your public key in the 'Key' box.
-
Finally, click on Add key to add it to GitLab. You will be able to see its fingerprint, the corresponding email address and creation date.
Associating your GPG key with Git
After you have created your GPG key and added it to your account, it's time to tell Git which key to use.
-
Use the following command to list the private GPG key you just created:
gpg --list-secret-keys --keyid-format LONG <your_email>Replace
<your_email>with the email address you entered above. -
Copy the GPG key ID that starts with
sec. In the following example, that's30F2B65B9246B6CA:sec rsa4096/30F2B65B9246B6CA 2017-08-18 [SC] D5E4F29F3275DC0CDA8FFC8730F2B65B9246B6CA uid [ultimate] Mr. Robot <your_email> ssb rsa4096/B7ABC0813E4028C0 2017-08-18 [E] -
Tell Git to use that key to sign the commits:
git config --global user.signingkey 30F2B65B9246B6CAReplace
30F2B65B9246B6CAwith your GPG key ID. -
(Optional) If Git is using
gpgand you get errors likesecret key not availableorgpg: signing failed: secret key not available, run the following command to change togpg2:git config --global gpg.program gpg2
Signing commits
After you have created your GPG key and added it to your account, you can start signing your commits:
-
Commit like you used to, the only difference is the addition of the
-Sflag:git commit -S -m "My commit msg" -
Enter the passphrase of your GPG key when asked.
-
Push to GitLab and check that your commits are verified.
If you don't want to type the -S flag every time you commit, you can tell Git
to sign your commits automatically:
git config --global commit.gpgsign trueVerifying commits
-
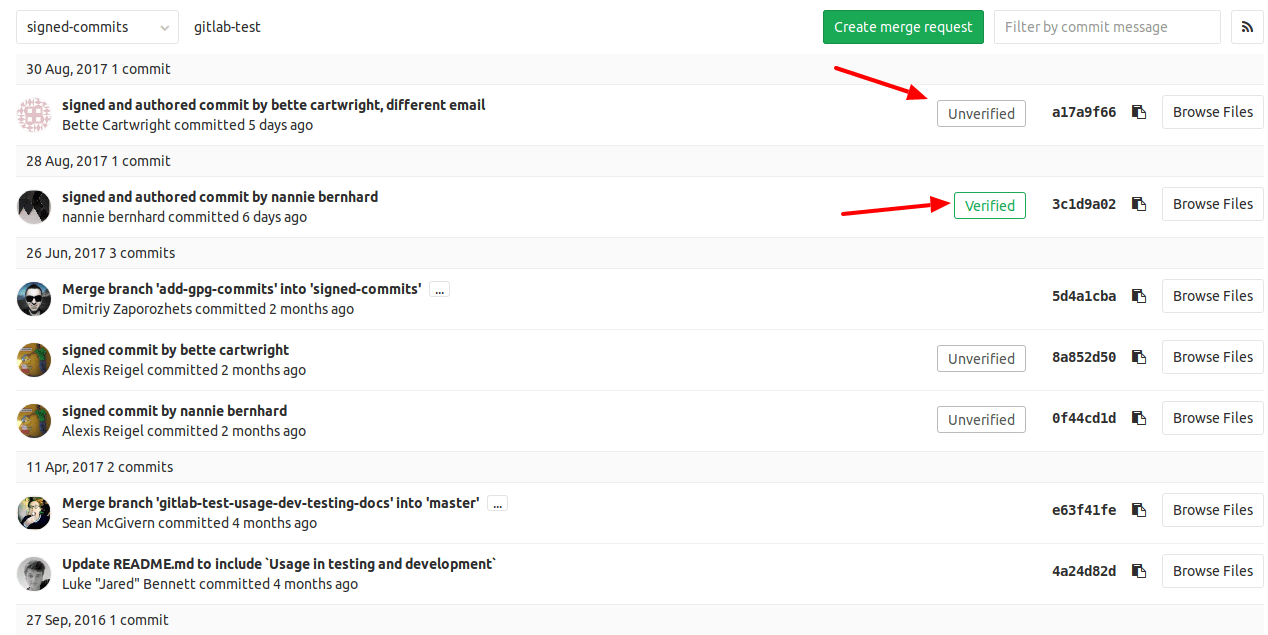
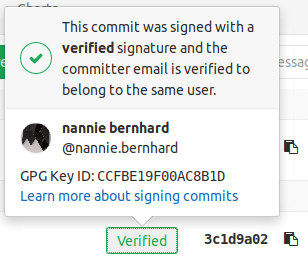
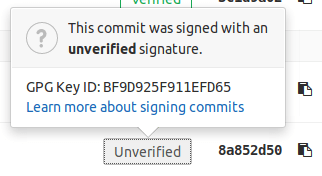
Within a project or merge request, navigate to the Commits tab. Signed commits will show a badge containing either "Verified" or "Unverified", depending on the verification status of the GPG signature.
-
By clicking on the GPG badge, details of the signature are displayed.
Revoking a GPG key
Revoking a key unverifies already signed commits. Commits that were verified by using this key will change to an unverified state. Future commits will also stay unverified once you revoke this key. This action should be used in case your key has been compromised.
To revoke a GPG key:
- On the upper right corner, click on your avatar and go to your Settings.
- Navigate to the GPG keys tab.
- Click on Revoke besides the GPG key you want to delete.
Removing a GPG key
Removing a key does not unverify already signed commits. Commits that were verified by using this key will stay verified. Only unpushed commits will stay unverified once you remove this key. To unverify already signed commits, you need to revoke the associated GPG key from your account.
To remove a GPG key from your account:
- On the upper right corner, click on your avatar and go to your Settings.
- Navigate to the GPG keys tab.
- Click on the trash icon besides the GPG key you want to delete.
Rejecting commits that are not signed (PREMIUM)
You can configure your project to reject commits that aren't GPG-signed via push rules.
GPG signing API
Learn how to get the GPG signature from a commit via API.
Further reading
For more details about GPG, see: